

Compliance
Delivering tomorrow’s standards, today
Rigorous governance
We fully protect our clients and experts with robust compliance frameworks and industry-leading risk management systems.
- Comprehensive policies: We adhere to strict policies covering data privacy, information security, and ethical conduct.
- Project oversight: Our dedicated global compliance team continuously monitors and updates our processes to reflect evolving risks.
- Compliance audits: We undertake regular audits to validate the effectiveness of our compliance measures.
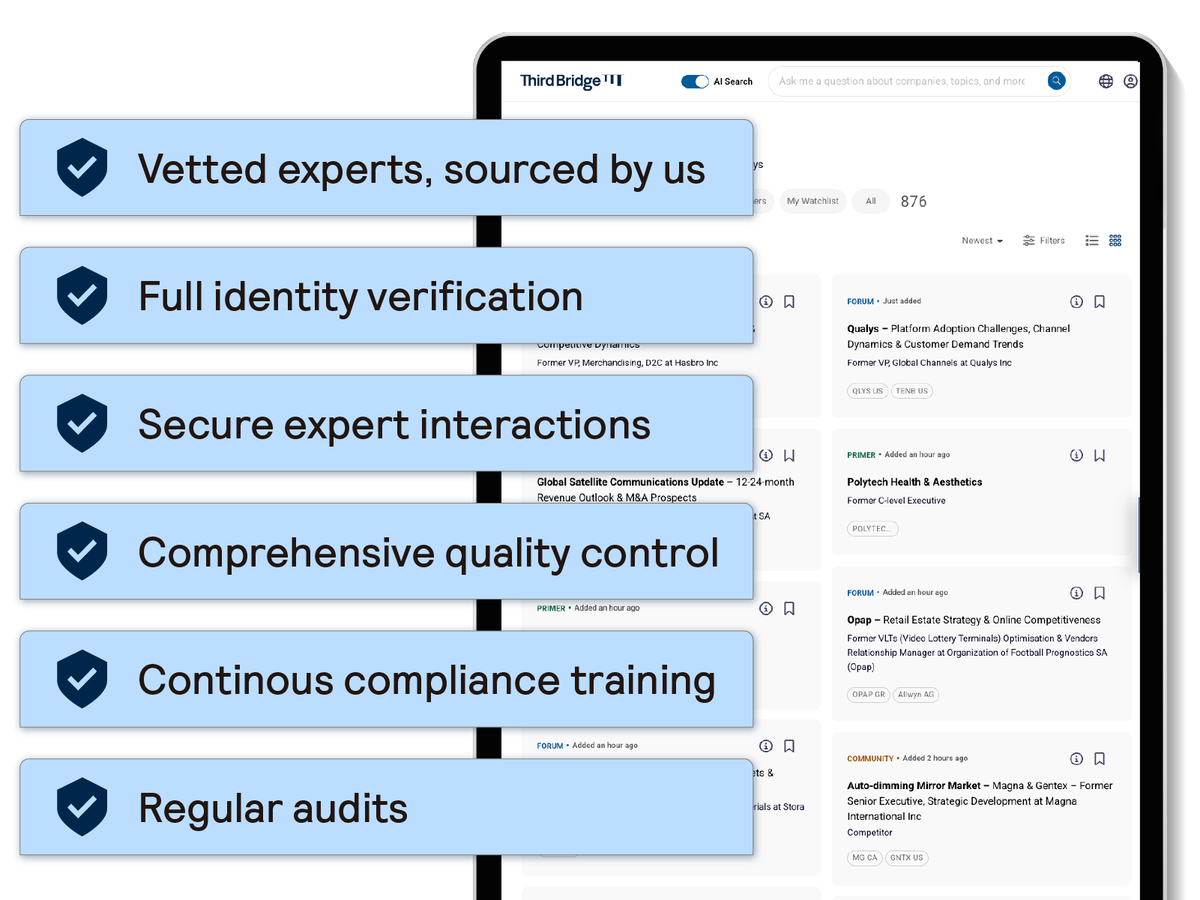
Secure expert interactions
We mitigate risk by applying robust checks to every expert interaction:
- Verified: We custom-source and background check all individuals when they first join our expert network, with additional checks for more active experts.
- Appropriate: Our experts are subject to compliance obligations through our terms of engagement and training. Clients can also add their own rules and requirements to ensure that every expert meets their specific compliance needs.
- Relevant: Our experts go through a strict vetting process to validate their relevant knowledge and experience.

Vetted content
Experts must meet our stringent compliance criteria in order to participate, and all of our content undergoes rigorous checks to prevent the disclosure of sensitive information.
- Expert qualification: Our extensive approval process is designed to filter out conflicted experts.
- Content review: We carry out both human and technology-enabled reviews of every transcript.
- Customizable controls: We provide customizable access features to ensure seamless alignment between your internal policies and our platform.

Assured technology
Information security is not just a technical requirement, it is a pillar of our commitment to our clients. We leverage a technology-led approach to ensure your data remains protected at every touchpoint.
- Industry-leading security certifications: We maintain ISO 27001:2022 and SOC 2 certifications. For our clients, this provides independent, third-party validation that our security controls meet the highest global benchmarks for data protection and operational integrity.
- Transparent security practices: We believe in radical transparency. You can visit our Trust Centre to download our latest security policies and compliance documentation, giving your internal risk teams the immediate evidence they need for vendor due diligence.
- Dedicated security expertise: Security is a continuous process, not a static state. Our global information security team continuously monitors, assesses, and enhances our security posture to protect the confidentiality, integrity, and availability of your data.

